No need to wait until Jan. 20th for results – we’ve got all the goods right here. Right now. So, if you’re tired of watching news highlights highlighting no news, keep reading. We put the spotlight on some major Expel updates around commodity malware and messaging.
Highlights
Commodity Malware
The term “commodity” is used to distinguish and group incidents resulting from installation of malicious software (i.e. malware) by targeted and non-targeted threats impacting workstations and servers. In fact, commodity infections have just as much potential impact to business operations as a targeted attack! These types of infections are opportunistic in nature aiming at user credentials or personal data for mass deployment of ransomware or cryptominer threats. No bueno.
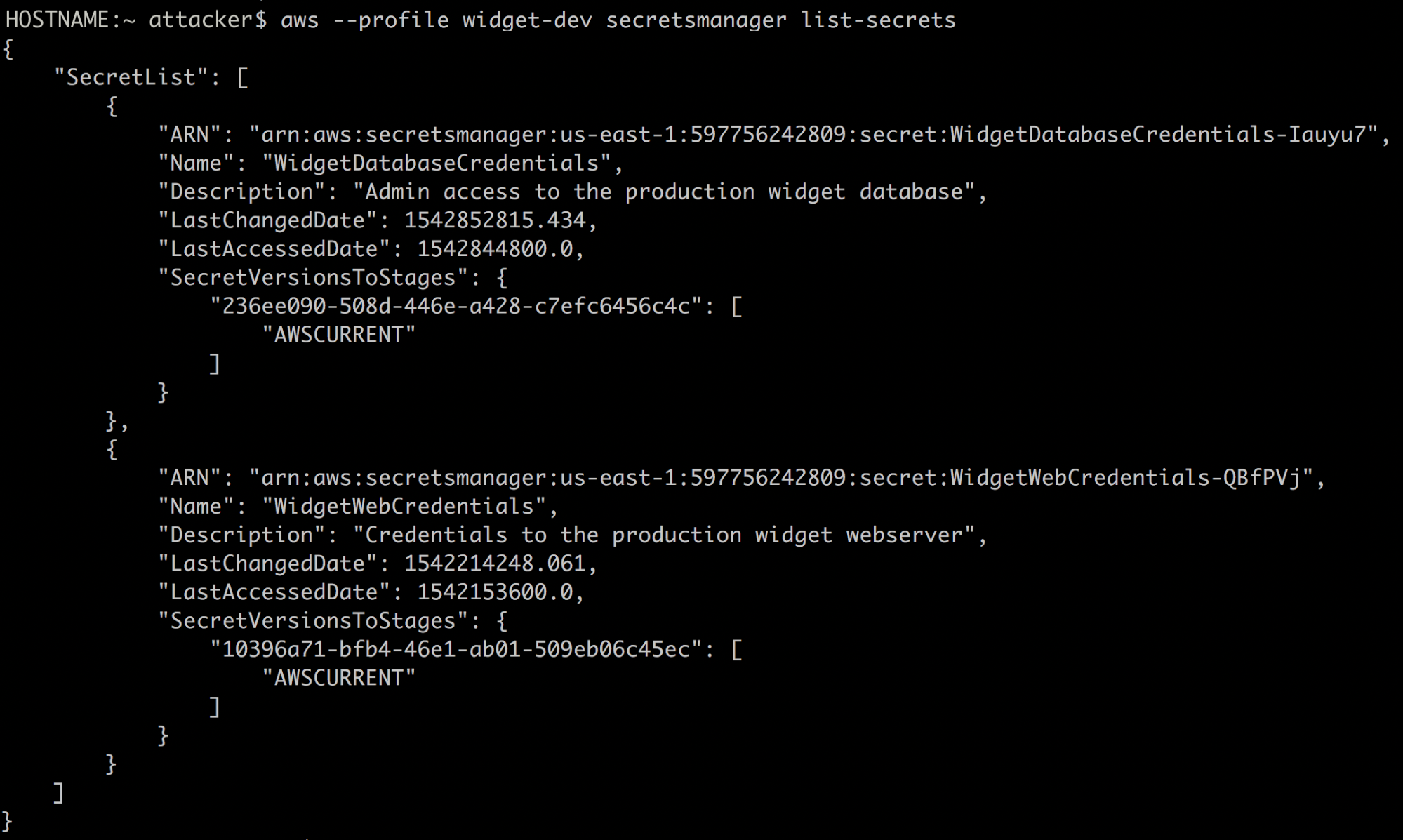
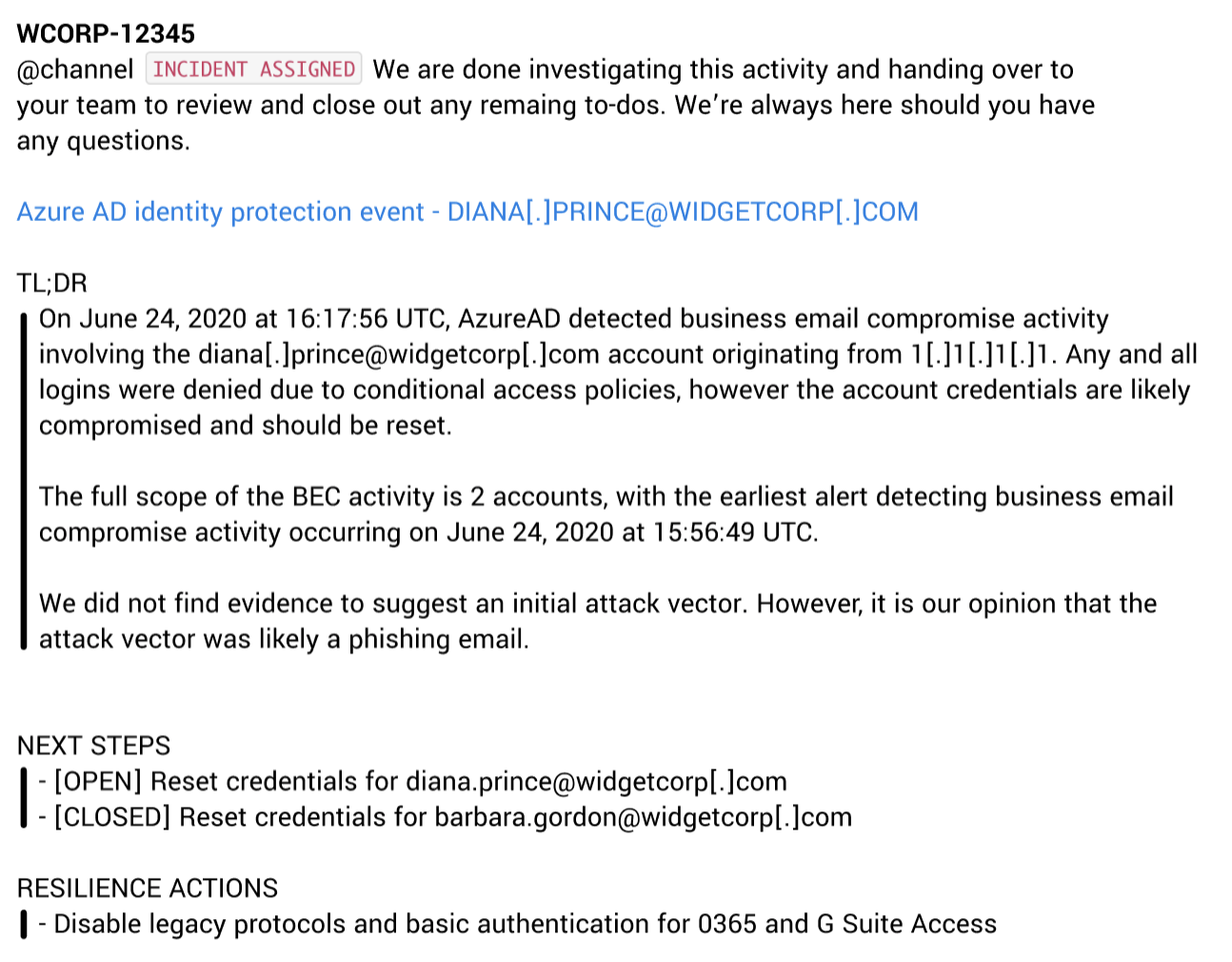
So, what did we do? We released a set of features that improve both the scale and quality for how we report commodity malware incidents. Feature updates include:
- A Commodity Malware Findings TL;DR which sheds light as to the origin, timing and scope of the incident
- An “alert-to-fix” timeline that so many of you have come to know and love
- An attack process tree for incidents triggered by EDR alerts
- An attack diagram that provides a visual for the hosts involved that should be addressed through remediation actions
New Automated Messages
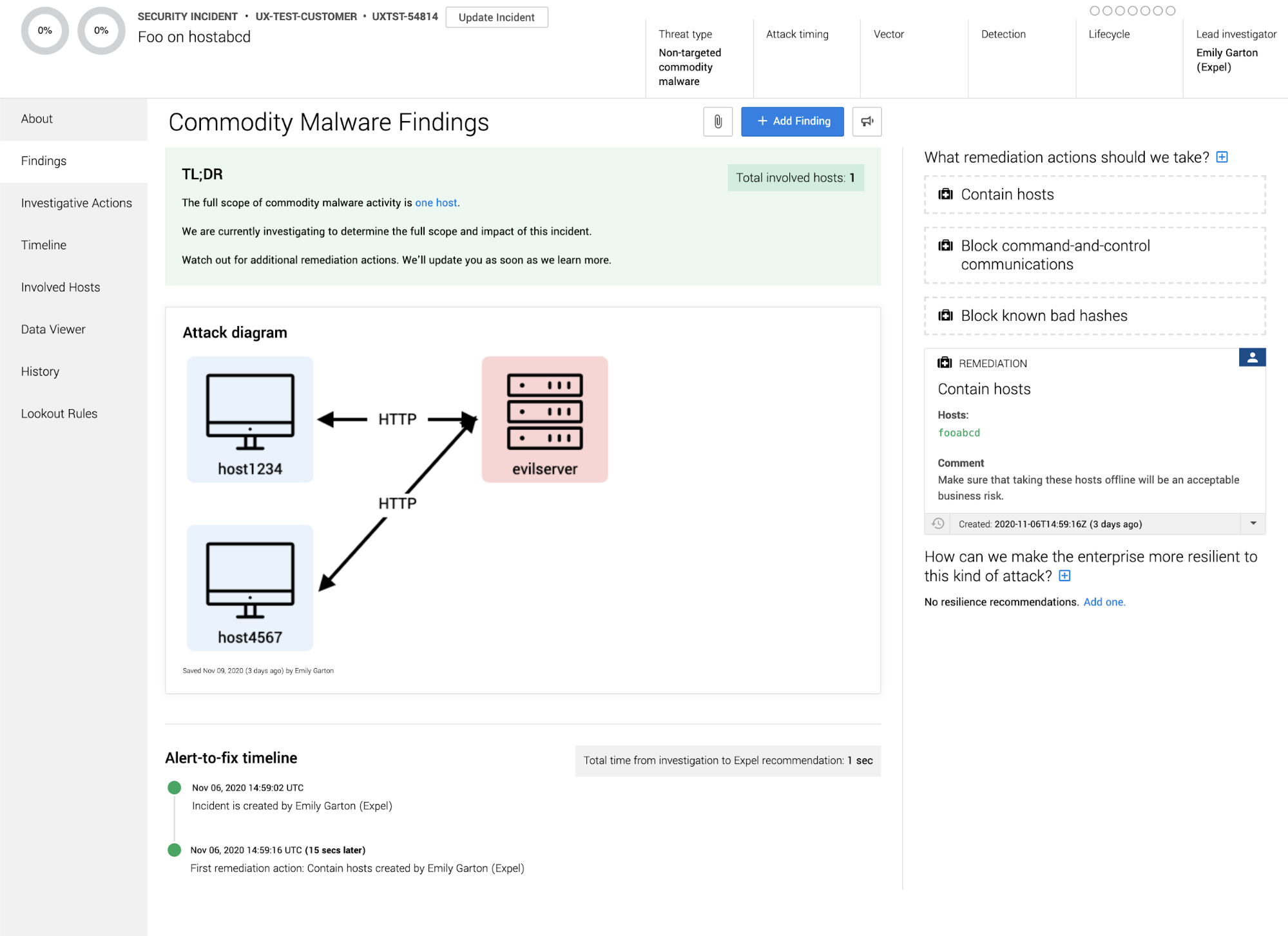
We love automation at Expel, so it shouldn’t come as a surprise that we’ve automated two additional messages for our SOC. Now, when an incident (think Business Email Compromise or Commodity Malware) is created, Workbench will send out a detailed Slack notification via RuxieTM containing incident name and link, initial summary details, next steps (remediation actions) and initial lead details. Not only do these automated messages provide you with a more robust summary than the “create incident” message, but they ensure more consistent notifications.
Other enhancements
- We added additional information to the summary banner at the top of incidents. Now you can see at a glance who is running the incident to ground.
- Our remediation actions have been updated so our analysts have more information about hash values that may need to be blocked.
- We’ve improved the new(ish) TL;DR feature on Business Email Compromise incidents.
- We changed the way we process alerts so we can get even more information into the hands of our analysts to help them make the right decisions on your behalf.
Other fixes (plus a few odds and ends)
- We removed some confusing options from the automatic investigative actions menus to reduce the cognitive load on our analysts (or yours) when running down leads.
- We noticed some recent framework updates for our front-end caused some elements to render in weird places. Yuck! This has been fixed.
- Some of our drop downs had gotten unwieldy and were running off the page. It was slowing us down, so yep – you guessed it – we fixed this.