Cloud security
Security operations | 2 min read
Expel x Google Cloud Next ‘24: pioneering next-gen cloud securityWe’re heading out to Google Cloud Next ‘24 to elevate the discussion around cloud security with cloud visionaries and thought leaders. Will you be there?
Security operations | 3 min read
No honor among ransomware criminalsAs the recent drama between the BlackCat ransomware gang and its affiliates shows, there’s no honor among thieves. Take steps to assess your org’s security now, so you can stay out of that kind of mess.
Security operations | 2 min read
Security alert: Ivanti Connect Secure and Policy Secure zero-day vulnerabilitiesThe Cybersecurity and Infrastructure Security Agency (CISA) believes threat actors are exploiting Ivanti Connect Secure and Policy Secure zero-day vulnerabilities. Here's what to know.
Security operations | 2 min read
Security alert: ConnectWise ScreenConnect 23.9.8 security fixVulnerabilities affecting ConnectWise versions 23.9.7 and prior leave self-hosted and on-premise ScreenConnect instances exposed to attackers. Here’s what happened and what can do about it now.
Security operations | 1 min read
GKE/Gmail vulnerability: notes and tipsSecurity researchers have discovered a new Google Kubernetes Engine misconfiguration. Here’s what you need to know.
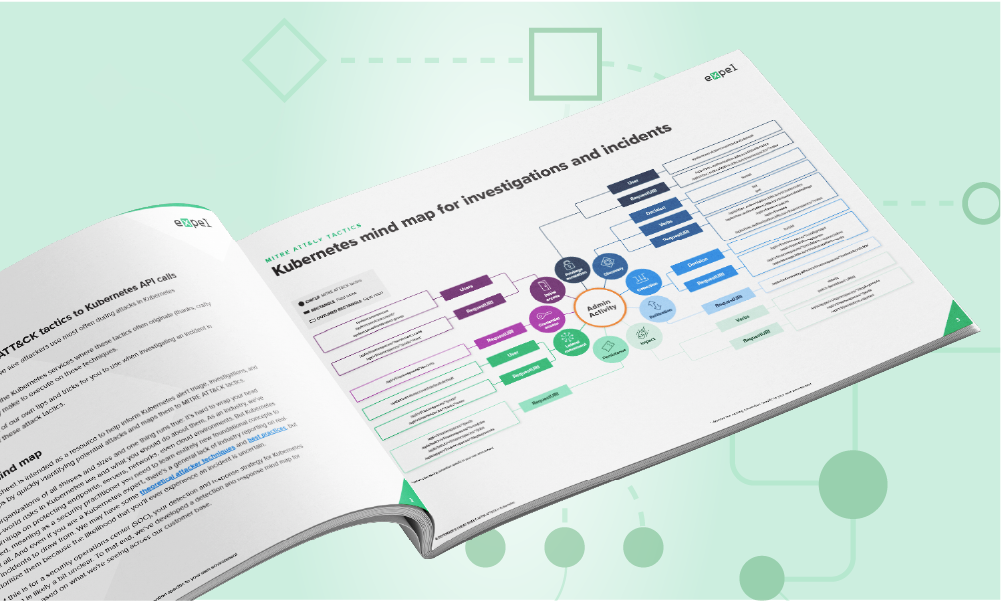
Security operations | 3 min read
New mind maps & cheat sheets: Azure & KubernetesOur new Kubernetes mind map/cheat sheet makes it easier for you to know which API calls are associated with different MITRE ATT&CK tactics in k8s environments.
Security operations | 3 min read
Following the lifecycle of a cloud alert in Expel WorkbenchOur new tour shows you the journey a cloud alert takes in Expel MDR for Cloud Infrastructure. It might just change how you think about securing your cloud (or multi-cloud) environment.
Security operations | 3 min read
Staff, C-suite disagree on how security drives innovationThe recent CSA research report found that the C-suite and security staff are disconnected on the role security plays in innovation. We want to explore why that’s happening.
Security operations | 3 min read
Expel Q3 Quarterly Threat Report: the top five findingsThe Q3 Quarterly Threat Report findings are based on incidents our security operations center identified in the third quarter this year. Here are a few of the top trends.
Security operations | 3 min read
In the Age of Innovation, Does Security Hold the Key?A new report by the Cloud Security Alliance, commissioned by Expel, showcases the results of research aimed at gaining a deeper understanding of several areas of innovation and cloud use trends.
Expel insider | 1 min read
Meet us at Infosec 2023Infosecurity 2023 is around the corner and we’re thrilled to be making our debut on the showfloor. Connect with Expel at Stand G90!
Security operations | 2 min read
Add context to supercharge your security decisions in Expel WorkbenchDefenders need so much information to make good security decisions in the SOC. Adding Context to Expel Workbench is one way to make faster and better decisions.
Expel insider | 3 min read
We’re definitely stronger together: top 3 takeaways from RSA Conference 2023Another RSA Conference is in the books. Take a look at what jumped out to us most from the event, and how we as defenders are all “Stronger Together.”
Expel insider | 1 min read
#RSAC round 2: Expel heads back to MosconeExpel is headed back to RSA Conference as an exhibitor for the second time. Stop by our booth to meet the crew, snag some swag, and let us show you security that makes sense.
Engineering | 3 min read
Integrations roundup: new integrations to manage overall business riskExpel has always used a bring-your-own-tech approach to security operations. Now our integrations are expanding beyond the sphere of cybersecurity and into some of today’s most popular business apps.
Security operations | 3 min read
Why MDR for Kubernetes environments is great news for your orgThis post discusses how managed detection and response (MDR) for Kubernetes environments helps organizations relying on in-house application development.
Security operations | 1 min read
Understanding the 3 Classes of Kubernetes RiskThe first step toward securing Kubernetes environments is understanding the risks they pose and identifying the ways in which those risks can be mitigated.
Security operations | 2 min read
Tell Dr. Kubernetes where it hurtsKubernetes is growing rapidly, and for important reasons. Like many new technologies, though, it faces growing pains. In part 1 of a series, Dan Whalen outlines the most common Kubernetes challenges.
Tips | 7 min read
So you’ve got a multi-cloud strategy; here’s how to navigate five common security challengesSwitching to a multi-cloud solution? Easy! Just kidding. Expel’s senior detection & response engineer shares some things you need to think about when going multi-cloud – and how to stay sane.
Engineering | 1 min read
So long, 2022! Our year in reviewTo mark the end of 2022 and the beginning of 2023, we’ve curated some of our favorite blog posts from the past 12 months.
Expel insider | 3 min read
5 cybersecurity predictions for 2023It’s that time of year when security folks gaze into the future and predict what’s on the horizon for 2023. Here’s what we think is up next for the cybersecurity industry in the new year.
Security operations | 4 min read
Dr. Strangelog or: How I learned to stop worrying and love alertsWhat if your data were higher in fidelity and context? We afford more refined alerts and embed more context and stability, assuming the tech is advanced enough to generate rich security signal.
Security operations | 3 min read
Expel Quarterly Threat Report Q3: Top 5 takeawaysOur third quarterly (Q3) threat report is here and it’s overflowing with cybersecurity data, trends, and recommendations to help you protect your organization. Here are our top five takeaways from Q3.
Security operations | 4 min read
Who ya gonna call (to make the most of your SIEM data)?Customers who import their SIEM to a tool like Workbench can translate all the hours invested in development into customized rules. In other cases, they may realize they no longer need a SIEM.
Security operations | 5 min read
Understanding role-based access control in KubernetesUnderstanding authorization is critical to knowing how role-based access control (RBAC) works for securing Kubernetes. No matter your skill level, you must understand the rules that govern Kubernetes.
Security operations | 3 min read
Three Kubernetes events worth investigatingMonitoring your Kubernetes environment is important — especially if you’re running production workloads. This post explains what you should be looking for once you’ve collected the audit logs.
Security operations | 3 min read
Kubernetes: the whale in the roomMore than half our cloud customers use Kubernetes (k8s), which can help companies ship software faster, avoid platform lock-in, and reap cost savings from elastic infrastructure that scales on demand.
Engineering | 3 min read
Connect Hashicorp Vault and Google’s CloudSQL databases: new plugin!Expel is excited to open source a new Hashicorp Vault plugin that brokers database credentials between Hashicorp Vault and Google’s CloudSQL DBs.
Expel insider | 3 min read
That’s a wrap! Top 3 takeaways from Black HatHacker Summer Camp (A.K.A Black Hat) felt especially energized this year, with more people, exhibitors, and fun. Read up on our takeaways from the show floor as first time exhibitors in Mandalay Bay.
Security operations | 3 min read
Top 5 takeaways: Expel Quarterly Threat Report Q2Our second quarterly (Q2) threat report is here and its chock full of cybersecurity data, trends, and recommendations to help you protect your organization. Here are our top five takeaways from Q2.
Security operations | 2 min read
A defender’s MITRE ATT&CK cheat sheet for Google Cloud Platform (GCP)In this new handy guide, we mapped the patterns we’ve seen throughout our GCP incident investigations to the MITRE ATT&CK Framework to help give you a head start protecting your organization.
Expel insider | 3 min read
Top 3 takeaways from RSA Conference 2022It was four days of excitement as we made our exhibitor debut at #RSAC. Now that we’ve had time to reflect on this year’s conference, here are three of the big takeaways from our time at Moscone.
Expel insider | 3 min read
RSA Conference Day 3: Impressions From the Show FloorDay three of the conference was full of interesting conversations with long-time industry folks who are no stranger to RSA. Here are some of our favorite takeaways and observations.
Security operations | 3 min read
Incident report: Spotting an attacker in GCPIn this report, we walk you through how an attacker gained access to a customer’s GCP environment, our investigative process, and some key takeaways for securing your organization.
Expel insider | 2 min read
RSA Conference Day 2: Inclusivity is the GoalAnother day at RSA full of interesting speakers, lessons learned, and (of course) cool swag — but one session stood out to us the most. Here are some of our main takeaways from day two.
Expel insider | 3 min read
RSA Conference Returns: Day 1 Keynote SummaryThat’s a wrap on day one of #RSAC and we’re still reeling from excitement. From beatboxers to keynote speakers, here are some of our takeaways from the first day at Moscone.
Threat intelligence | 3 min read
Expel Quarterly Threat Report: Cybersecurity data, trends, and recs from Q1 2022Top takeaways from our first quarterly report, filled with patterns and trends we identified from Q1 2022. Our goal? Help translate the events we detect into a security strategy for your organization.
Expel insider | 2 min read
Meet us at Moscone… Expel makes its #RSAC debut!For the first time, Expel is headed to RSA Conference as an exhibitor! Stop by our booth to meet the crew, snag some swag, meet Josie and Ruxie, and let us show you that security can be delightful.
Security operations | 6 min read
Incident report: From CLI to console, chasing an attacker in AWSOur SOC detected and stopped unauthorized access in one of our customer’s AWS environments. Here’s how we spotted it, the steps we took to understand what they did, lessons learned and key takeaways.
Security operations | 5 min read
Evaluating MDR providers? Ask these questions about their onboarding processLooking for an MDR provider? Make sure you understand their onboarding process. Here are the questions you should ask when you’re evaluating MDRs. Bonus: learn how we do onboarding here at Expel.
Tips | 3 min read
5 pro tips for detecting in AWSCloud-based infrastructures can be confusing, but sometimes building a better security program starts with the basics. Try these pro tips to help focus the lens for detecting threats in AWS.
Security operations | 4 min read
Attack trend alert: AWS-themed credential phishing techniqueThey’re at it again. This time attackers are phishing for credentials by sending fake AWS log-in pages to unsuspecting users. Find out how our crew identified and triaged a phishing email.
Expel insider | 2 min read
Great eXpeltations 2022: Cybersecurity trends and predictionsIntroducing Great eXpeltations 2022: Cybersecurity trends and predictions — an annual report from our security operations center (SOC) on top threats, how to handle them, and what to expect this year.
Engineering | 5 min read
Threat hunting: Build or buy?Not sure if you should build your own hunting capability or get a hunting partner? Check out this post to discover your options and the things you should consider (yes, we break down cost for you).
Security operations | 4 min read
What’s threat hunting and is it worth it?Heard about hunting but are unclear on whether it’s something you should invest in? You’re not alone. Find out what it is and the value it brings to your org’s detection and response capabilities.
Expel insider | 4 min read
More good news in still unusual timesWe’ve reached a valuation over $1 billion thanks to our Series E fundraising round, led by CapitalG. Check out what our founders have to say about this exciting news and what’s next for Expel.
Security operations | 6 min read
Swimming past 2FA, part 2: How to investigate Okta compromiseFirst we showed you how to spot an Okta compromise in this two-part blog series. Now we’ll walk you through our investigation and share five tips on how you can strengthen your security defense.
Security operations | 6 min read
How Expel goes detection sprinting in Google CloudBuilding detections in Google Cloud Platform (GCP) but not sure where to start? Time to get strategic. Our detection and response engineers demystify the process for building detections in the cloud.
Security operations | 9 min read
Well that escalated quickly: How a red team went from domain user to kernel memoryA red team recently swooped in and showed off some new tactics. What started as a PowerShell download cradle quickly turned into a custom rootkit download. Find out how we spotted the crafty red team.
Security operations | 4 min read
Swimming past 2FA, part 1: How to spot an Okta MITM phishing attackCrafty attackers are finding new ways to bypass multiple-factor authentication. Find out how our SOC detected an attack and get some tips on how your org can prevent credentials phishing.
Security operations | 7 min read
Cloud attack trends: What you need to know and how to stay resilientWe shared the top attack trend spotted during the pandemic and what to keep an eye out for looking ahead. But how do you remediate and stay resilient against these attacks? Our crew shares some tips.
Security operations | 3 min read
Expel Hunting: Now in the cloudWe’ve added something new to Expel Hunting: cloud hunts. Find out how our crew’s newly developed hunting techniques can help you spot visibility gaps in your cloud (and give you some peace of mind).
Security operations
The top cybersecurity attack trend we saw emerge during the COVID-19 pandemicCheck out our newest infographic to learn about the top attack trend during the COVID-19 pandemic, how our SOC’s data reinforces these recent findings and how you should be looking ahead.
Engineering | 11 min read
Migrating to GKE: Preemptible nodes and making space for the Chaos MonkeysFind out how Expel’s internal teams collaborated to migrate our core infrastructure from a legacy environment to GCP, with no downtime (while also making sure they were prepared for a little chaos).
Engineering | 6 min read
5 best practices to get to production readiness with Hashicorp Vault in KubernetesFlying blind when it comes to running Hashicorp Vault in Kubernetes? We’ve got you covered. Accelerate your path to production without compromising on security with these tips and best practices.
Engineering | 8 min read
Containerizing key pipeline with zero downtimeMigrating to Kubernetes as Expel’s core engineering platform with zero downtime – and without interfering with our analysts’ workflow – is a tall order. But our engineers pulled it off. Find out how.
Engineering | 12 min read
Behind the scenes: Building Azure integrations for ASC alertsFind out how Expel’s internal teams built an integration on top of Azure signal – creating a new detection strategy for ASC that provides more context around alerts and improves customer visibility.
Expel insider | 3 min read
Introducing Expel Workbench™ for Amazon Web Services (AWS)We’re excited to announce the launch of our first SaaS product! It automates the investigation of AWS alerts and logs – allowing your team to spend less time finding and fixing security issues.
Security operations | 1 min read
Got workloads in Microsoft Azure? Read thisGot Microsoft Azure? Running Microsoft products in your org? Then you might want to get a free copy of our all-new Azure guidebook.
Engineering | 7 min read
Plotting booby traps like in Home Alone: Our approach to detection writingFind out how Expel’s D&R engineers think about detection writing, and how this process helps our SOC analysts make smart decisions and gain a deeper understanding of our customers’ environments.
Threat intelligence | 6 min read
Supply chain attack prevention: 3 things to do nowWhat do you do when you can’t trust the internet? Supply chain attacks like the SolarWinds Orion breach are not new. Here are some things you can do to help prepare and guard against similar attacks.
Security operations | 3 min read
The SolarWinds Orion breach: 6 ideas on what to do next and whyHere are some of our early observations on the SolarWinds Orion breach, plus our ideas on what to do next to detect related activity and better protect your org.
Security operations | 6 min read
Evilginx-ing into the cloud: How we detected a red team attack in AWSRed team sneak attack? Bring it on. Find out how we tackled a red team attack using open source offensive security tools in AWS and what you can do to protect your org from similar attacks.
Security operations | 2 min read
Introducing a mind map for AWS investigationsWe’ve been doing a lot of investigations in AWS using CloudTrail logs and have been noticing some interesting things along the way. So we created an AWS mind map for our team (and you). Check it out!
Engineering | 8 min read
The power of orchestration: how we automated enrichments for AWS alertsAutomation is key when it comes to helping analysts focus on doing what they do best – investigating legitimate threats. Find out how we use orchestration to automate enrichments for AWS alerts.
Engineering | 8 min read
Terraforming a better engineering experience with AtlantisTo build something useful you must first understand your users. Find out how Expel used Terraform and Atlantis to build a platform that makes self-service provisioning in cloud infrastructure easy. % %
Security operations | 8 min read
Behind the scenes in the Expel SOC: Alert-to-fix in AWSWonder what real-life investigation and response looks like in the cloud? Buckle up! Our team walks you through a coin-mining attack in AWS that they recently foiled – all the way from alert to fix.
Security operations | 8 min read
Why the cloud is probably more secure than your on-prem environmentIs your data really safer in the server room next door? Probably not. Here are five reasons why the cloud offers better security than your on-prem environment.
Security operations | 3 min read
Where does Amazon Detective fit in your AWS security landscape?If you’re running workloads on AWS, then you’ll want to know all about the latest and greatest AWS-native security tools. We’ve got you covered in our latest post.
Security operations | 5 min read
Making sense of Amazon GuardDuty alertsIf you’re running workloads on AWS, then you’d better be running GuardDuty. But what is it and how can you make sense of all the signals? Here are our pro tips.
Security operations | 7 min read
Generate Strong Security Signals with Sumo Logic & AWS CloudtrailLooking to get more or better security signals from AWS Cloudtrail? Learn how with Expel.io. See how we use the Sumo Logic SIEM for actionable data.
Security operations
Here’s what you need to know about business email compromise (BEC)How often does a business email compromise actually happen? And what should you do about it? Our infographic answers those questions and more.
Security operations | 5 min read
This is how you should be thinking about cloud securityYour IT team isn’t racking and stacking servers like they used to, but cracking the cloud security code is easier than you think. Get our pro tips for doing just that.
Tips | 4 min read
Four common infosec legal risks and how to mitigate themThere are four missteps we see happen often that open fast-growing companies up to unnecessary legal risks -- here’s how to course correct.
Security operations | 7 min read
How to build a useful (and entertaining) threat emulation exercise for AWSWant to test your analysts’ detection skills in the cloud? Here are our tips and tricks for building your own threat emulation exercise in AWS.
Tips | 4 min read
How public-private partnerships can support election securityElection security measures (or lack thereof) are making headlines. How can private sector orgs contribute to public sector security? Our CISO Bruce Potter’s got some ideas.
Tips | 8 min read
How to find Amazon S3 bucket misconfigurations and fix them ASAPWhy do Amazon S3 bucket breaches happen and how can you protect your own org from making this mistake? We’ve got all the AWS pro tips for you in our latest post.
Tips | 10 min read
Seven ways to spot a business email compromise in Office 365Learn what business email compromise is, BEC scams categories, and how to prevent or identify these spam phishing attacks in Office 365 including mailbox rule examples and more.
Security operations | 3 min read
Three tips for getting started with cloud application securityIf you're feeling like your SaaS security knowledge is a bit cloudy, these three pro tips will get you started on the right path.
Security operations | 3 min read
Office 365 security best practices: five things to do right now to keep attackers outHere are five Office 365 security best practices to check out right now.
Security operations | 7 min read
Getting a grip on your cloud security strategyUnderstanding how to think about cloud security differently is half the battle. At Expel, we've thought a lot about it, and we’ve identified three key points that should inform your cloud strategy.